The 30-Day Integration Inventory That Stops Silent Data Loss
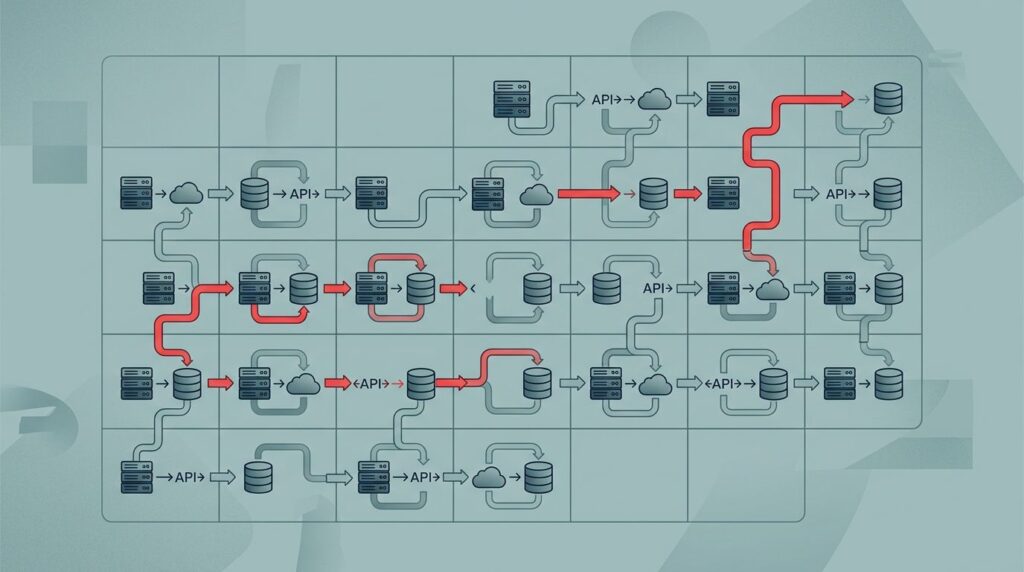
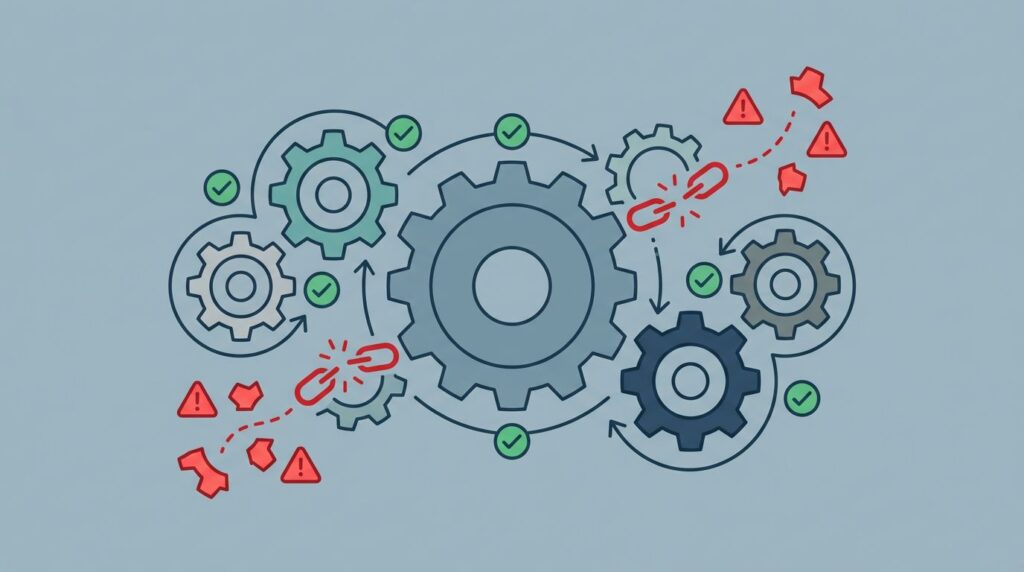
You rarely catch silent data loss when it happens. You feel it later, when reports don’t match, staff re-enter records, or a client update disappears in the data flow between systems. That kind of failure looks small, but it spreads fast. A 30-day integration inventory uses inventory integration to catalog connections, reveal assumptions, and spot […]
The 30-Day Integration Inventory That Stops Silent Data Loss Read More »