If you're a new audit chair, you've probably already lived this meeting. Management presents a cyber update. The slides are clean. The acronyms are dense. The CISO talks through vulnerabilities, blocked attacks, training completion, and a few red-yellow-green boxes. Everyone nods.
Then the meeting ends, and a basic question still hangs in the air.
Are we getting better or worse at managing cyber risk?
That is the test of board cyber risk reporting. Not whether the board packet exists. Not whether the committee heard an update. Whether directors can understand the company's exposure, make decisions, and hold management accountable for reducing the right risks.
Most reporting fails that test because it was built for documentation, not governance. It reports motion instead of meaning. Worse, even when the report surfaces a serious issue, many organizations still haven't defined who owns the next decision. So the board hears the risk, management notes it, and nothing moves.
A strong board cyber risk reporting system does three things. It translates technical conditions into business impact. It shows trend and direction, not just point-in-time status. And it assigns clear ownership for what happens after the meeting.
The Board Meeting Where Confidence Goes to Die
The deck says a lot. The room learns very little.
The CISO walks the committee through patched vulnerabilities, phishing attempts blocked, endpoint coverage, and recent policy updates. A director asks whether third-party exposure is rising. Another asks whether the company's most important systems would stay available during a serious incident. The answers drift back to tools, ticket queues, and security projects already underway.
Nobody is incompetent in that room. The problem is simpler. The report is speaking one language, and the board needs another.
Boards can look satisfied and still be underinformed. Boards report 82% satisfaction with CISO reporting on regulatory trends, yet only 47% feel CISOs can articulate the impact of evolving threats, a 35-percentage-point gap that shows how compliance visibility can mask weak risk understanding, according to IANS research on board and CISO strategic dialogue.
What directors are actually trying to learn
A board doesn't need a tour of security operations. It needs answers to a short list of governance questions:
- Exposure: What could hurt the business most right now?
- Direction: Is that exposure increasing, stable, or decreasing?
- Preparedness: Are our controls and response capabilities strong enough for the risks we carry?
- Trade-offs: Where should management spend time and money next?
- Accountability: Who owns the fix, and when does the board see progress?
If the report can't answer those questions, it isn't board-ready.
Good reporting reduces uncertainty. It doesn't just prove that activity happened.
Why this feels worse for a new audit chair
A new chair often inherits a reporting pattern that nobody wants to challenge. The packet is established. The cadence exists. The committee has a routine. Changing it can feel disruptive.
But keeping a weak format is more dangerous than disrupting it. A vague report creates false comfort. It lets everyone say cyber was discussed, while leaving the board exposed if a material event occurs and someone later asks what directors understood.
That is where confidence starts to die. Not in the breach. In the meeting before it, when everyone had information but not clarity.
Why Most Board Cyber Reporting Fails
The usual diagnosis is wrong. This isn't mainly a dashboard problem. It's a framing problem, a translation problem, and an accountability problem.
Most board cyber reporting fails because it answers the wrong question. It tells the board what the security team did. It doesn't show whether those actions reduced meaningful business risk.
Activity is not the same as risk reduction
Security teams often work hard and still report badly. A 2023 survey found that 90% of CISOs still struggle to communicate the actual business value of their security programs, with the root problem being activity reporting instead of outcome reporting, as described in AwareGO's analysis of cybersecurity metrics for the board.
That distinction matters.
A board learns almost nothing from metrics like:
- Volume counts: 5,000 phishing emails blocked
- Patch counts: 200 CVEs remediated
- Tool coverage: endpoint agent installed on most devices
- Training completion: annual awareness module assigned
Those may be useful operating metrics. They are not governance metrics unless they connect to reduced exposure, improved resilience, or clearer financial consequence.
A better report asks different questions. Did the phishing intervention reduce staff susceptibility? Did patching materially reduce the likelihood of compromise in systems the business depends on? Did a control investment improve containment capability? Did a vendor issue create a risk to revenue, service delivery, or customer trust?
Boards need business language, not security theater
The board's job is resource allocation and oversight. Directors don't need a tour through every control. They need the implications.
That's why a board packet full of technical data often creates a strange mix of reassurance and unease. The report feels substantial. The content feels operational. But directors still can't judge whether management is reducing the right risks or just staying busy.
If you're shaping this from the chair side, ask one blunt question after every major slide: So what changed in the company's risk position?
That one question exposes weak reporting fast.
For a practical baseline on what management should be bringing forward, this guide on what a board should expect to see in a cyber risk report from management is a useful reference point.
The hidden failure is after the meeting
Even good reporting can die in the handoff.
The committee hears that a critical third-party dependency is weak, or that a key business process lacks resilient controls, or that incident response capability is uneven across units. Then the room moves on because nobody has defined who turns that board discussion into an approved decision.
That is the ownership vacuum. The CISO identifies the issue. Finance controls budget. Operations controls execution. The board expects movement. Nobody owns the integrated response.
Practical rule: Every board-level cyber risk finding should end with a named owner, a decision deadline, and a stated path for escalation.
Without that, board cyber risk reporting becomes a compliance ritual. You can minute the discussion, archive the deck, and still fail to govern the risk.
What this failure costs leadership
Weak reporting doesn't just waste time. It creates business damage in slow motion.
- Misallocated spend: Management funds visible projects instead of the controls that reduce the most important exposure.
- Shallow oversight: The board hears updates but can't challenge assumptions or test trade-offs.
- Poor prioritization: Security, IT, finance, and operations argue from different data and different definitions.
- Weak defensibility: If regulators, insurers, investors, or diligence teams ask what the board knew and when, the paper trail may show cadence without insight.
That's why I push leaders to stop asking for more metrics and start asking for sharper ones. Better governance comes from fewer measures, better framed, tied to actual decisions.
A Board-Ready Cyber Risk Reporting Framework
A useful board report needs structure. Not more slides. Not more tooling. Structure.
The simplest model I've found is a five-pillar frame that forces management to move from technical noise to decision-grade signal. If a cyber update doesn't cover these five areas, the board is usually missing something material.

Pillar one overall risk posture
Start with the big picture. The board should know the organization's current cyber risk posture in plain language, with a view of whether financial exposure is moving up or down.
The most critical metrics for board reporting now center on the likelihood of cyber events and their potential financial severities, and frameworks like FAIR help translate technical exposure into business terms, according to Kovrr's guidance on board cybersecurity metrics.
Many teams still go wrong. They open with control status. The board needs exposure first.
Weak version:
- We completed vulnerability scans across core infrastructure.
Strong version:
- Management's current view is that the company's highest cyber exposure remains concentrated in customer-facing systems, core identity infrastructure, and key vendor dependencies. Estimated loss severity differs by scenario, and management is prioritizing the areas where control improvements would reduce the most financial exposure.
If you're modernizing the architecture underneath these discussions, resources on implementing Zero Trust in small businesses can help management connect identity, access, and segmentation decisions to real risk reduction rather than vague modernization language.
Pillar two top risks and threat relevance
Don't brief the board on every threat in the news. Brief them on the few threat scenarios that matter to your business model.
A logistics company, a healthcare services firm, and a SaaS platform should not present the same cyber narrative. The relevant question isn't "what are attackers doing?" It's "which scenarios could interrupt how we make money, serve customers, or protect trust?"
Use this part of the report to name the top risks clearly:
- Operational disruption: Could ransomware or system unavailability stop fulfillment, scheduling, claims, care delivery, or customer support?
- Data exposure: Could a breach trigger legal, contractual, or trust consequences tied to sensitive information?
- Third-party concentration: Could one vendor failure disrupt a critical business process?
- Identity compromise: Could privileged access misuse create broad internal damage?
Keep this section short. Boards don't need a threat intelligence feed. They need a business relevance filter.
If management can't explain why a risk matters to revenue, service delivery, reputation, or legal duty, it probably isn't ready for the board.
Pillar three controls maturity and effectiveness
Controls matter. But the board shouldn't get a shopping list of tools.
It should see whether the control environment is maturing against a recognized framework and whether the controls that matter most are effective where the business is most exposed. NIST CSF is a sound reference point because it gives leadership a common structure without drowning the committee in technical detail.
This is also where many teams confuse "implemented" with "working."
A control can exist on paper and still fail in practice. A good board report distinguishes among design, operating effectiveness, and business coverage.
Examples of board-useful questions include:
- Framework alignment: Which control domains remain weakest against the chosen framework?
- Coverage quality: Do critical assets and core business processes have the same level of protection, or are there blind spots?
- Exception handling: Where has management accepted risk, and why?
- Third-party controls: Are vendor controls being trusted blindly or validated meaningfully?
A fractional advisor, internal security leader, or a governance partner such as CTO Input can help management map operational evidence to board-level narrative so the committee sees control maturity in business context rather than as a compliance checklist.
Pillar four incidents and near misses
This section should be honest, short, and analytical.
Boards need to know what happened, what it affected, how management responded, and what changed because of it. Near misses matter because they reveal control weakness before a public event does.
Don't sanitize this section into harmless trivia. If a vendor outage exposed concentration risk, say so. If privileged access controls delayed containment, say so. If an incident response process worked well, explain why it worked and what should be repeated.
The test here is simple. Could a director leave the meeting understanding whether the organization is learning?
Pillar five roadmap and key indicators
A board report should end by connecting risk to action.
That means showing the current roadmap, the major decisions management needs, and the few indicators that tell the board whether the program is improving. In such reporting, trend matters far more than volume.
Use indicators that help directors judge movement, discipline, and resilience. Show whether remediation is happening fast enough, whether major dependencies are being addressed, and whether response capability is becoming more reliable.
This section should also make the asks explicit. If management needs funding, operating support, policy approval, or cross-functional enforcement, say it directly.
From technical noise to business signal
| Pillar | Weak Metric (Activity) | Strong Metric (Outcome) |
|---|---|---|
| Overall risk posture | Number of scans completed | Change in estimated exposure across the most important cyber scenarios |
| Top risks | List of current threat alerts | Business-specific scenarios most likely to disrupt operations, trust, or key revenue processes |
| Controls maturity | Number of tools deployed | Degree of control effectiveness across critical assets and business processes using a recognized framework |
| Incidents and near misses | Count of alerts investigated | What happened, what was learned, and which control or process changes reduced repeat risk |
| Roadmap and indicators | Project status updates | Evidence that priority actions are reducing exposure, improving resilience, or closing board-recognized gaps |
This framework works because it gives the board a full system view. Exposure. Relevance. Readiness. Learning. Action. That's what board cyber risk reporting should do.
Structuring the Narrative from Dashboard to Decision
A strong content model still fails if the delivery is clumsy. Boards don't read cyber reports the way security teams build them. They need a short narrative, a logical sequence, and a dashboard they can trust.
The report should work as a decision tool first and a reference packet second.

Build the deck in layers
The first slide should carry the whole argument.
If the CEO, audit chair, and one independent director only read one page before the meeting, that page should tell them current posture, top shifts since last quarter, material incidents or near misses, and the decisions management needs from the board or committee.
After that, keep the sequence tight:
- Executive summary: current posture, trend, major changes, required decisions.
- Top risk scenarios: the few risks that matter most to this business right now.
- Control effectiveness and maturity: where the control environment is strong, weak, or uneven.
- Incident and near-miss review: lessons from recent events.
- Roadmap and asks: priorities, dependencies, decisions, ownership.
- Appendix: operational detail for directors who want to go deeper.
That structure respects the board's time and keeps the discussion above the tool level.
Design the dashboard for trend, not decoration
Most cyber dashboards are overbuilt. Too many colors. Too many widgets. Too many metrics with no threshold logic behind them.
Use fewer measures. Define them clearly. Show trend over time. Tie thresholds to the board's stated risk appetite.
Mean Time to Detect and Mean Time to Respond are more useful to a board than raw vulnerability counts, but only if the organization uses standardized definitions validated by governance, because inconsistent definitions make trend analysis unreliable, as explained in Kovrr's analysis of boardroom cybersecurity metrics.
That point is bigger than it sounds. If one team defines an incident one way, a vendor reports it another way, and internal operations apply a third standard, the dashboard becomes fiction. Directors see trend lines. Management sees argument.
For leaders working through this problem more broadly, this piece on technology dashboards that turn tech spend into clear decisions is useful because the same reporting discipline applies outside security too.
What good board narration sounds like
The presenter should sound like an operator, not a product demo.
Bad narration:
- We rolled out a new tool.
- Coverage improved.
- The team handled a high volume of alerts.
- We're tracking remediation.
Good narration:
- The company's most significant exposure remains concentrated in a small number of scenarios.
- One area improved because a targeted control reduced risk in a critical business process.
- Another area worsened because a dependency remains unresolved.
- Management needs a decision on priority, funding, or risk acceptance.
The board does not need proof that security is busy. It needs proof that management understands the risk and is steering it.
Keep the appendix, but don't lead with it
Technical detail still matters. It just doesn't belong at the center of the board discussion.
A clean appendix lets directors inspect assumptions, definitions, major initiatives, framework mappings, and supporting evidence without turning the main discussion into a technical review session. This matters for defensibility too. If the board asks how management reached a conclusion, the evidence should exist and be easy to trace.
Use explicit decision prompts
Every board cyber risk report should contain direct prompts like these:
- Decision needed: approve, defer, or reject a proposed investment or remediation path.
- Risk acceptance needed: confirm whether a known exposure sits within or outside current tolerance.
- Escalation needed: assign a cross-functional owner when the issue spans security, IT, operations, finance, or legal.
- Follow-up needed: specify what management will return with at the next meeting.
A report that lacks decision prompts usually turns into a passive briefing. Passive briefings rarely change the company's risk position.
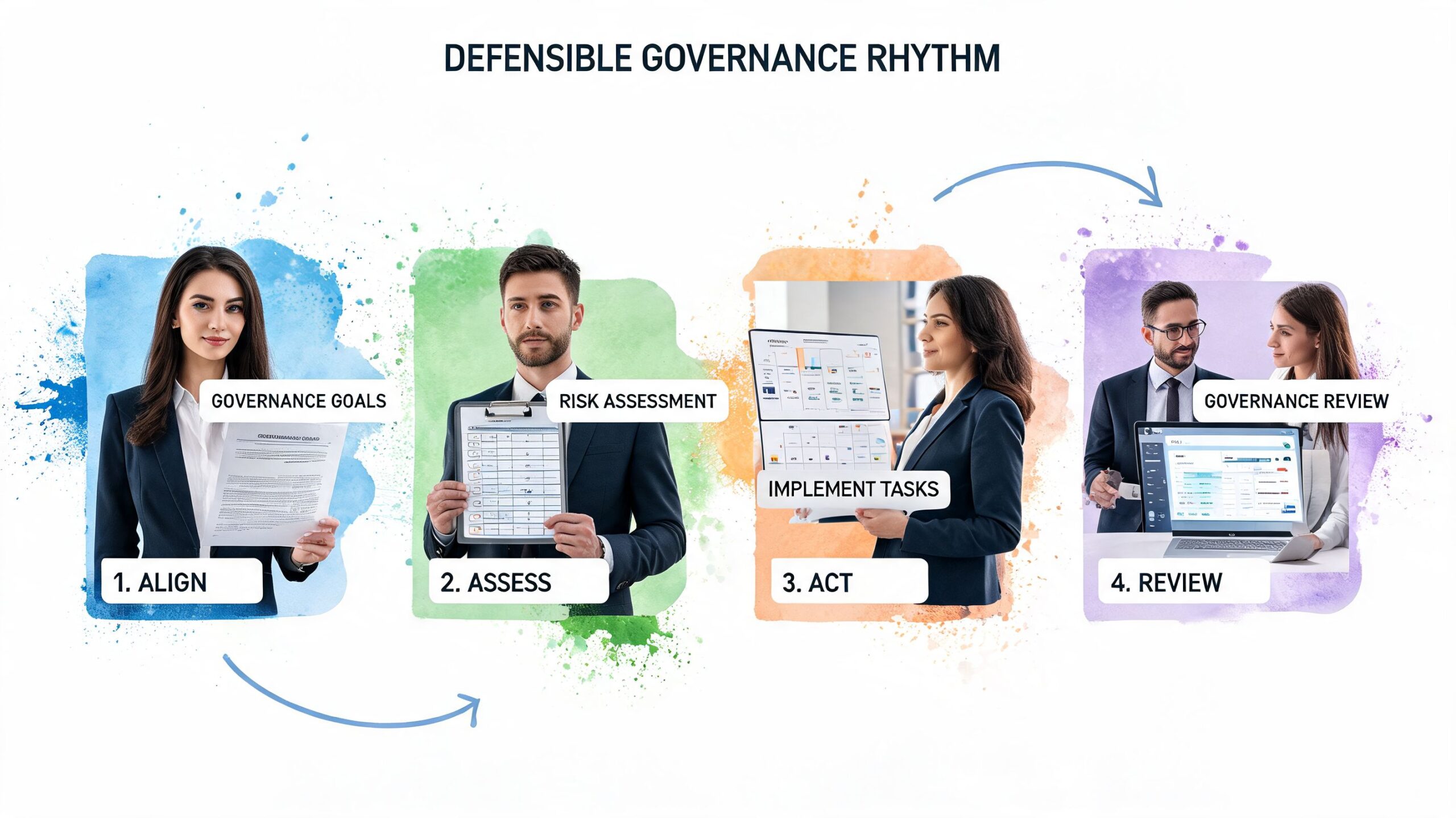
Building a Defensible Governance Rhythm
One good deck won't fix a weak governance system. The board needs a repeatable rhythm that makes cyber oversight inspectable, useful, and calm.
That rhythm has three parts. Cadence. Ownership. Evidence.
Set the cadence and keep it boring
Cyber risk should not reach the board only when there's a crisis.
Leading practice is clear. Boards should receive substantive cyber risk updates at least quarterly, with an annual deep dive based on a framework like NIST CSF, according to Deloitte's guidance on cybersecurity board reporting.
That cadence matters because it turns cyber into a standing governance topic instead of an adrenaline event. Directors can see trend. Management can show whether investments are changing exposure. The company can document that oversight is real and regular.
If you want an additional operating lens on how cadence supports governance, these Paradigm International risk insights are useful for thinking about risk reporting as part of a broader leadership discipline.
Clarify who owns what after the meeting
Most organizations still break in this area.
The CISO may own the analysis. The CIO may own infrastructure execution. The COO may own business process changes. The CFO may control budget. Legal may own disclosure questions. The audit chair may expect movement across all of it.
Write down the decision rights.
- Report owner: Who assembles the data and maintains metric definitions?
- Narrative owner: Who converts the data into a board-level risk story?
- Decision owner: Who has authority to approve remediation, accept risk, or escalate conflict?
- Execution owner: Who is accountable for completing the action once a decision is made?
- Committee follow-up owner: Who tracks open actions back to closure?
Without that map, board cyber risk reporting can look mature while execution stays sloppy.
For a more focused view on cadence and committee structure, this article on board risk committee cyber reporting cadence is worth reviewing.
Make the evidence trail inspectable
If the board packet says risk is improving, management should be able to show why. If it says a control is effective, there should be evidence behind that statement. If metrics changed, the definitions should be stable enough to support comparison.
That doesn't mean dumping raw logs into the board binder. It means building traceability from source data to management summary to board conclusion.
A defensible reporting system lets an outsider follow the chain from evidence to judgment without guessing.
Questions the chair should ask every quarter
Use the Q&A period as a stress test, not a courtesy round.
- What changed since the last meeting that matters most to the business?
- Which risk remains outside tolerance, and what is blocking action?
- What assumptions in this report are weakest or least certain?
- Where are metrics hard to trust because definitions or sources are inconsistent?
- Which cross-functional action needs my committee's backing to move?
Those questions move the conversation out of status mode and into governance mode.
What Better Looks Like Calm Confident Oversight

In a well-run boardroom, cyber isn't a mystery and it isn't theater.
The committee knows the few risks that matter most. Management explains them in business terms. Directors can see whether exposure is moving in the right direction. When something worsens, they know why. When management asks for money or priority, the case is tied to risk reduction and resilience, not fear.
The tone changes too. Fewer defensive explanations. Better questions. Faster decisions.
That only happens when the last gap is closed. The decision-to-action bottleneck is what turns many decent reports into useless ones. Governance frameworks and SEC-related expectations describe how boards should be informed, but they often leave decision rights unclear. Organizations that define those rights between the board, the CISO, and the CFO turn reporting into an execution system, as discussed in Skadden's analysis of emerging board expectations.
The practical result
When this works, the CISO stops looking like a technical messenger and starts acting like a business risk leader.
The board stops asking for more detail because it finally has the right detail. Audit and risk committees stop revisiting the same unresolved issue every quarter. Management meetings after the board session get shorter because ownership is already clear.
That is the outcome of mature board cyber risk reporting. Not prettier dashboards. Better decisions, fewer surprises, and a calmer operating environment.
Your Next Step Toward Clearer Reporting
If your board packet creates more motion than clarity, don't treat it as a formatting issue. Treat it as a governance issue.
Weak board cyber risk reporting usually means the organization hasn't aligned its metrics, narrative, decision rights, and follow-through. That's why the same issues keep resurfacing, budget debates stay muddy, and directors still feel uneasy after the meeting.
Start by reviewing your next board cyber update against four questions. Does it show business impact, trend, decision needs, and named ownership? If not, fix that before you add another chart.
If your board is asking harder cyber questions and the answers still feel vague, CTO Input can help you diagnose the reporting and decision bottlenecks behind that problem. A clarity call is a practical way to identify where ownership is fuzzy, where reporting loses meaning, and what to change first so oversight becomes calm, defensible, and useful.

