You do not buy cybersecurity because you enjoy more software or another round of meetings. You buy it because weak security turns into lost time, lost trust, and avoidable cost.
The real question is not whether hackers exist. It is whether your business can afford the delay, disruption, and cleanup when controls are thin. That is why cybersecurity as a business investment has to be judged by revenue, uptime, contracts, and leadership control.
If your team is already dealing with sloppy reporting, vendor sprawl, and too many workarounds, the bill is probably showing up before any incident does. Here is a practical way to judge whether the spend makes sense for your business.
Key takeaways
- Cybersecurity protects more than data. It protects uptime, customer trust, cash flow, and your ability to keep promises.
- Weak security often costs money before a breach. Downtime, rework, and duplicate tools are part of the bill.
- The right spend depends on what you cannot afford to lose, and how much disruption you can live with.
What cybersecurity actually protects in your business
Cybersecurity protects the parts of the business you cannot afford to lose for a day. That includes uptime, customer trust, cash flow, contracts, and your credibility with the board.
A system outage during billing, a locked account that stalls operations, or a vendor with too much access can cost far more than the tool that caused it. The issue is not just stolen data. It is the business damage that follows when systems stop working or people stop trusting what they see.
Risk is not always dramatic. Sometimes it looks like missed deadlines, messy vendor sprawl, weak reporting, or recovery work no one planned for. Those problems drain attention long before they hit the news.
The hidden costs you feel before a breach
Most companies feel weak security in ordinary ways first. You see more manual work, more approvals, more duplicate tools, and more time spent reconciling what should already line up. Then the team starts building workarounds. Then decisions slow down.
The real bill often shows up as delay, rework, and surprise spending, not a clean line item called weak security.
If you keep paying through overtime, cleanup, and missed deadlines, you are already funding the problem.
Prevention usually looks boring. Cleanup never does.
Why risk grows as your business grows
More systems, more users, more customers, more vendors, more data. Each one adds another path into your environment. If growth happens faster than ownership, your attack surface expands while accountability gets fuzzier.
That is where executive technology leadership matters. You do not need more motion. You need someone who can see the whole setup, decide what matters, and keep the business from adding blind spots as it scales.
A small company can sometimes survive on heroics. A growing company cannot do that for long.

How to tell if your business is already paying for weak security
You are already paying for weak security if projects keep slipping because access, approvals, or vendor dependencies slow things down. You are paying if your team spends hours reconciling systems that should talk to each other. You are paying if leaders cannot tell which risks are real and which are just noise.
That cost is often buried inside overtime, rework, delayed launches, and the extra consulting that comes in after the fact. It does not always appear on a budget line with a neat label. But it shows up in your margins.
The question is not whether you can point to a breach. The question is whether the business is already absorbing the drag.
When reporting is weak, risk stays invisible
If the reporting is vague, the risk stays vague. And vague risk is expensive.
Leadership cannot make good calls when no one can explain what changed, what is blocked, what got riskier, and who owns the next step. That is true for the board, the executive team, and the people doing the work.
You do not need more technical detail for its own sake. You need reporting that helps you act. If the information does not change a decision, it is not helping you.
This is where stronger visibility matters most. When the board can see what matters, it can fund the right things before the bill gets bigger.
When vendor control is low, your risk gets higher
When vendors start driving the roadmap, security gets harder to manage. Tool sprawl creates gaps between systems. One supplier controls identity, another handles backups, another owns data sync, and nobody owns the whole picture.
That is a governance problem as much as a technology one. A vendor can own the implementation. They should not own the business decision.
If you do not have strong internal ownership, fractional CTO services can help you sort out priorities, accountability, and which vendor promises deserve scrutiny. That matters because the business does not fail in a neat, single-point way. It fails where the handoffs break.
What a good return on cybersecurity looks like
A good return on cybersecurity looks like fewer disruptions, faster recovery, better audit outcomes, stronger customer confidence, and less stress at the leadership table. You are not buying perfection. You are buying control.
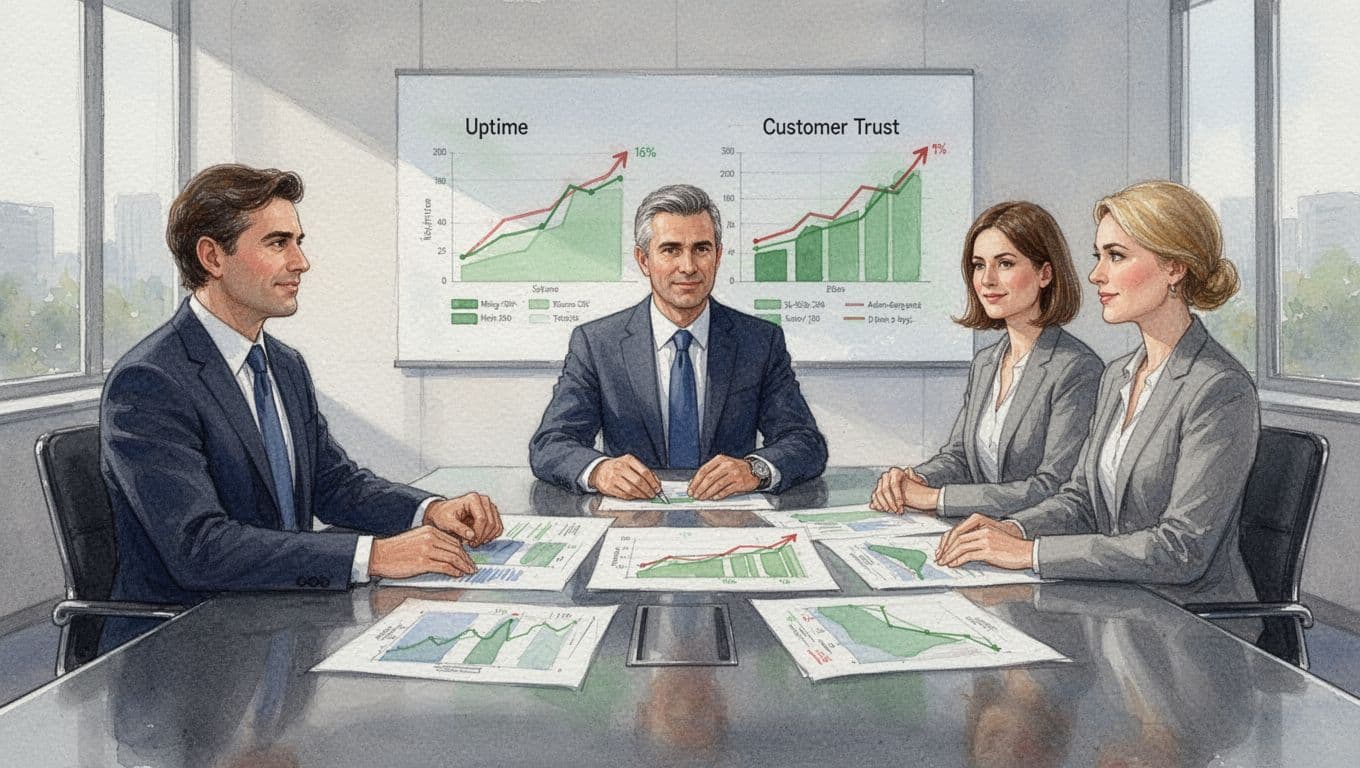
The payoff is often stability, not headlines
The payoff is often what does not happen. No outage that turns into a weekend fire drill. No ransomware panic that scrambles your team. No compliance failure that forces rushed spending. No board meeting where everyone is guessing.
That is the value of cybersecurity as a business investment. It keeps ordinary weeks ordinary.
You notice it when recovery is orderly, when the team knows what to do, and when leaders are not spending three days explaining what went wrong. Stability does not sound flashy, but it protects margin and decision quality.
Cybersecurity helps you move faster with less fear
Good security does not have to slow the business down. In the right setup, it speeds things up. When systems, controls, and ownership are clear, your team can make decisions faster because they trust the guardrails.
Leaders spend less time chasing updates. Teams spend less time guessing. The result is cleaner execution and fewer surprises.
If your business needs clearer visibility into delivery, spend, and risk, services for technology oversight is the kind of support that keeps security tied to business decisions, not just technical cleanup.
How to decide what level of investment makes sense
The right spend depends on your size, industry, data sensitivity, customer expectations, and how much disruption you can survive. A healthcare group and a professional services firm do not need the same controls. A company with payment data and one with public content do not carry the same exposure.
The better question is not, “How much should I spend?” It is, “How much risk am I willing to keep?”
Start with your most valuable assets
Start with the things that would hurt most if they were exposed or lost, customer data, uptime, intellectual property, access to money, and compliance obligations. Those are the first places your security dollar should go.
If you protect low-value areas first, you buy comfort instead of control. That feels busy, but it does not move the business forward.
Match your security spend to your real risk
Do not buy random tools to feel better for a quarter. Start with the gaps you can name, the assets you can see, and the losses you cannot absorb. Right-sized security beats scattered security every time.
If technology decisions feel scattered or too dependent on the wrong people, Get an Executive Technology Clarity Check can help you sort out what needs to happen first.
The smartest first steps if you are unsure where to begin
You do not need to fix everything at once. Start with the risks that could hit hardest, such as weak access control, poor backups, exposed vendors, missing incident ownership, or reporting no one trusts.
Then ask three simple questions for each one. Who owns this? How would we know it failed? What would it cost us if it did?
That gives you a clean way to separate noise from the stuff that deserves money now.
Focus on the biggest risks first
You do not need a perfect plan to begin. You need to stop pretending every issue has the same weight.
If one weak point could stop billing, expose customer data, or trigger a board-level problem, start there. If the board asks for a risk view, give them the things that matter most, not a pile of technical detail they cannot act on.
If you want a better sense of when outside leadership makes sense, talk to a fractional technology executive and get the issue named before you spend more on tools.
Bring in outside help when leadership is stretched
If no one clearly owns security, or if your team is already overloaded, outside executive support can save you months of guessing. That is especially true when the problem is leadership, not effort.
A lot of businesses need a senior guide who can connect risk, vendors, reporting, and priorities before the next bad surprise lands. You do not need drama. You need clarity.
Conclusion
Yes, cybersecurity is worth the investment when you care about protecting growth, trust, and control. If you only look at the budget, you will miss the larger cost, which is delay, confusion, and weak ownership.
The real choice is not whether to spend. It is where to spend so the business gets safer, steadier, and easier to lead.
Start with your biggest risks. Decide what matters most. Then invest where it protects the business, not just where it adds another tool.

