A grant pays for a pilot, the team likes it, and the renewal slips into next year’s budget. That sounds harmless, until tool sprawl starts running your operations.
You end up with extra logins, duplicate data, side workflows, and reports nobody fully trusts. Managing multiple logins and duplicate data creates hidden costs that erode operational efficiency. Worse, each “temporary” tool adds cost, risk, and one more thing leadership has to explain. The fix starts before the next pilot goes live, to prevent tool sprawl from impacting IT operations.
Key takeaways
- Grant-funded pilots often become permanent because nobody sets an exit decision, owner, or sunset plan.
- Tool sprawl shows up first in reporting, duplicate work, weak ownership, and growing vendor dependence.
- You can stop it by embracing tool rationalization, treating every pilot like a time-bound business decision, not a free extra that leads to redundant tools.
Why grant-funded pilots so often become permanent tool sprawl
Most pilots don’t fail because the tool is bad. They fail because the rules around the tool are weak, underscoring the need for strong IT governance to manage new tools effectively.
A grant lowers the pain of the first purchase. That makes it easy to say yes. However, the grant rarely pays for the hidden parts, training, integrations, admin time, data cleanup, vendor oversight, and the cost of keeping one more system alive after the pilot ends.
Then the pilot starts spreading, fueling digital transformation across teams. One team uses it first. Another team adopts it because it seems helpful. Soon, nobody wants to turn it off because work now lives inside it, making it part of your organization’s digital infrastructure.
This is where tool sprawl stops being a tech issue and becomes a leadership issue. If nobody owns the decision, the default is renewal. If nobody defines success, “people seem to like it” becomes the standard. If nobody plans the exit, the pilot writes itself into your operating model.
You can see the budget impact of data silos in the data silo tax in post-award grant management. Disconnected systems don’t only waste money. They slow decisions and muddy accountability.
A pilot without a sunset rule is not a pilot. It’s a future renewal line.
Spot the signs before renewal season locks them in

The warning signs show up long before anyone says “we have tool sprawl.” You usually feel them first in drag and confusion.
Maybe your team enters the same client or program data twice. Maybe reports pull different numbers from different systems. Maybe one grant tool now handles work that should sit in a core system. Meanwhile, a few staff members become the only people who know how the pilot works, fostering shadow IT.
Another clue is weak offboarding. When a pilot ends, can you move the data, shut off access, and explain what happens next? If not, you don’t have a pilot. You have an undeclared dependency that creates cybersecurity vulnerabilities and widens your attack surface.
Finance often feels this before IT does. Invoices for SaaS applications multiply. Contract dates drift. Discounts expire. Nobody can say which tools are mission-critical and which ones are leftovers from old funding.
If that sounds familiar, a fast self-review like the intake-to-outcome clarity checklist can help you surface where tools, handoffs, and reporting are breaking down. The same pattern shows up across functions, including fundraising, where IT tool audits like the fundraiser’s tool audit can expose overlap that drains budget and focus.
Build a pilot exit plan before you launch the next one
The best time to stop tool sprawl is before the contract starts. You need a simple decision frame, not a long policy binder.
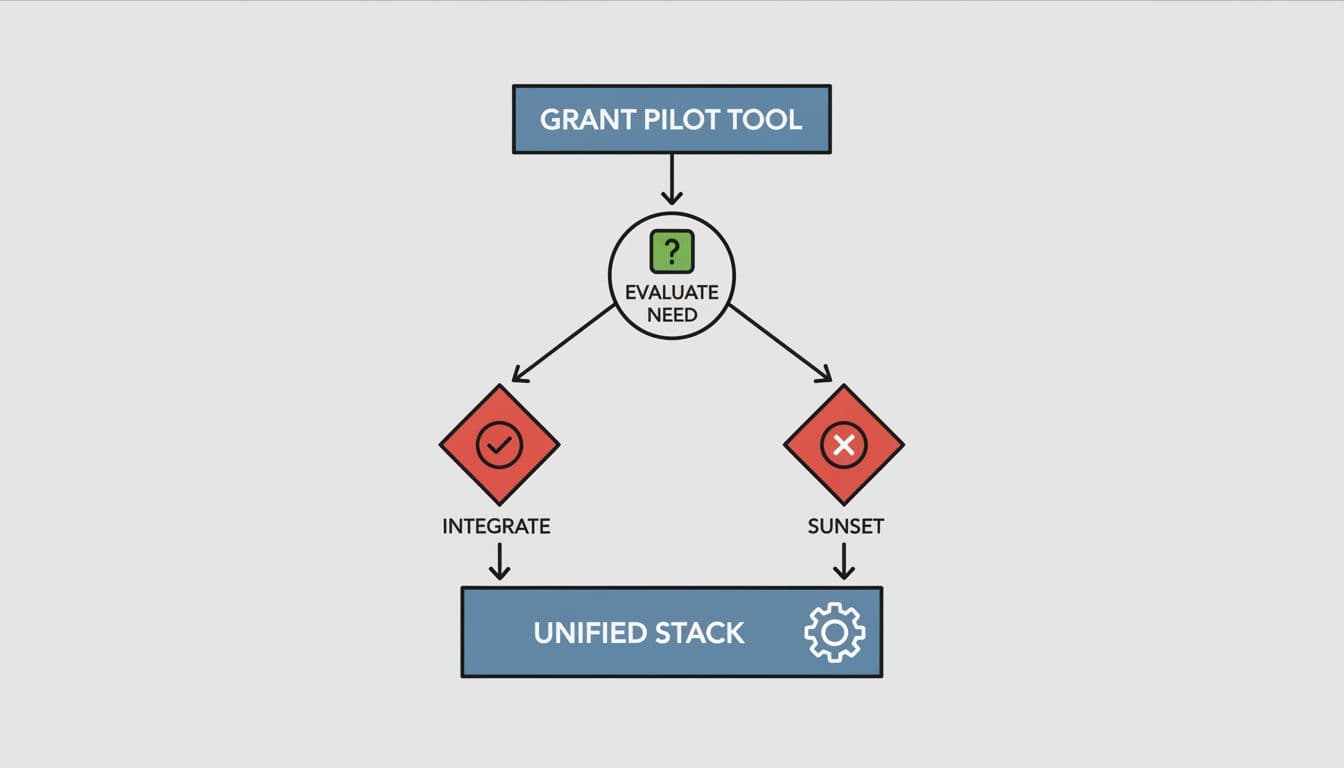
Start with four decisions:
- Define the business problem first. Name the pain in plain language. For example, slow intake, weak referral follow-up, or poor grant reporting.
- Set one owner. A pilot needs a decision owner with authority, not a loose group that meets when it can.
- Pick the exit date at the start. Before launch, set the date when you will keep, integrate, replace, or shut down the tool.
- Plan the sunset path. Decide how data moves, who loses access, what workflow management changes, and what happens if the pilot does not earn a permanent place.
Those four moves change the whole conversation. You stop asking whether people like the tool. You start asking whether it solved the problem at a reasonable cost.
For many mission-driven teams, this works best inside a short, business-first roadmap. A practical technology roadmap for legal nonprofits shows the right pattern, map reality, name tradeoffs, and sequence the decisions. If you want proof that cleanup pays off, these legal nonprofit tech case studies show how overlapping systems can quietly drain serious dollars through license costs until someone steps in for tool consolidation and simplifies the tech stack.
FAQs
How many pilot tools are too many?
There isn’t a magic number. The real limit is your ability to govern them. Tool sprawl brings alert fatigue from too many systems, making SIEM, IAM, and incident response harder to manage while weakening your security posture. If ownership, reporting, and renewals are blurry, you already have too many.
Should you ban grant-funded pilots?
No. Pilots can help you test ideas without betting the whole operation. The problem isn’t testing. The problem is keeping tools that never earned a permanent role.
Who should decide whether a pilot stays?
One executive owner should make the call with input from operations, finance, program, and IT. Shared input helps. Shared ownership usually blurs the decision and fuels tool sprawl.
How does tool sprawl affect IT productivity and security?
Excess pilot tools create tool sprawl that hampers IT productivity by widening skill gaps in areas like observability, automation, and data integration. Without centralized management, it also degrades your security posture through fragmented oversight and risk management gaps.
A grant should give you room to test, not a back door for permanent sprawl. When you treat pilots like temporary experiments with clear owners and end dates, you keep control.
That means fewer tools, clearer visibility, higher IT productivity, and better decisions under pressure.
In your next leadership meeting, ask one blunt question: if this grant ended tomorrow, which pilot tools would you keep, and why?