A policy exception should be rare. When it shows up every week, it stops being an exception and starts becoming your real operating model.
That shift is easy to miss because each exception feels reasonable on its own. Yet over time, side deals, one-off approvals, and silent workarounds create policy drift, unintended non-compliance, weaker oversight, and decisions you can’t defend with confidence.
Key takeaways
- Policy exception management should protect flexibility, not hide flaws in the policy exception process.
- Repeated exceptions usually point to a bad policy, a weak process, or missing ownership.
- If you don’t track expirations, risk, and repeat patterns, exceptions will run the business.
- Proactive risk exception management identifies when a standard no longer fits operational reality.
When the work around becomes the rule
Most exception trouble starts with a good reason. A vendor needs temporary access amid third-party risk management concerns. A staff member skips a step to hit a deadline because legacy systems often trigger the need for a security exception. A leader approves a one-time workaround because the alternative feels slower.
Then it happens again. And again.
Soon, the formal policy sits in a binder while the real rule lives in email, chat, and memory. Nobody sees the full list. Nobody knows which exceptions expired. Staff learn that the fastest path is submitting an undocumented exception request instead of fixing the issue.

This is how organizations slide into quiet disorder. The shoulder becomes the road. In high-trust settings, that cost grows fast. The same patterns show up in technology challenges for legal nonprofits, where small breaks turn into reporting chaos, dropped handoffs, and data sprawl.
If the same exception keeps coming back, you don’t have an exception. You have an unowned rule.
Why poor policy exception management costs more than compliance
Weak policy exception management doesn’t only create regulatory compliance pain. It also slows work, skews priorities, and rewards whoever pushes hardest.
For example, if intake rules get bypassed for “urgent” cases but nobody logs why, you lose the signal that demand is outgrowing capacity. Logging reasons for exceptions improves risk analysis and helps define your organization’s risk appetite. If referral steps get skipped, teams stop trusting status reports. If a vendor keeps special access “for now,” your risk picture gets softer than reality. These patterns highlight operational risk. The intake-to-outcome clarity checklist is useful here because it helps you spot where exceptions are masking broken flow.
This also becomes a trust issue. Boards, funders, and senior leaders don’t want perfect systems. They want honest visibility into the risk assessment process. When exceptions live off the books, reporting gets weaker. Ownership gets blurry. Decisions take longer because nobody knows which rule still applies.
That matters even more when you handle sensitive information and information security is at stake. The recent data protection best practices for nonprofits makes the point clearly: temporary workarounds around client data can undermine data protection and create lasting exposure.
Build a policy exception management process people will follow
The answer isn’t more paperwork. It’s a small, visible policy exception process that your team can easily follow under pressure.
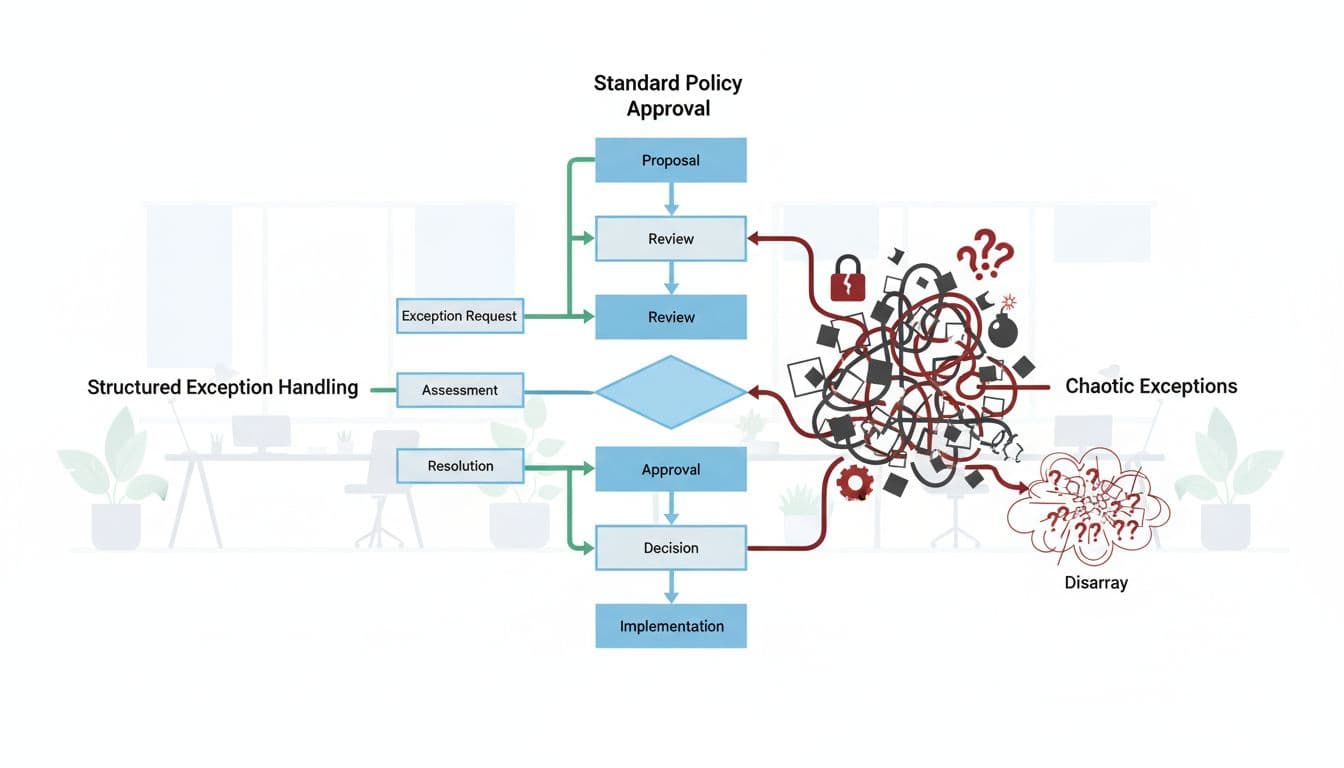
A workable exception process needs five basics:
- One request form: Put all exceptions through one request form, not side chats.
- One decision owner: Name the Chief Information Security Officer or establish a tiered approval process to decide who can approve, who advises, and who records the result.
- One risk statement: Document the risk acceptance and what compensating controls cover the gap.
- One end date: Set expiration dates so every exception expires unless someone renews it.
- One visible log: Keep a central record that leaders can review quickly.
That structure sounds simple because it is. Simplicity matters. If your process is too heavy, people will route around it. A plain approval model, like the one outlined in this policy exception approval process, works better than a dense policy nobody uses.
Also, connect exception data from exception requests to real fixes. Fixing root causes is essential for maintaining a strong security policy and developing a risk mitigation strategy. If the same issue appears month after month, push it into a real plan. A practical technology roadmap for legal nonprofits shows the right mindset: map reality, decide what matters first, then fix the root cause instead of letting the workaround become permanent.
Review exceptions like debt, not paperwork
Every exception creates debt. Some debt is worth taking, especially when mitigating factors are documented during the review. But debt needs an owner, a review date, and a payoff plan.
So review your log at least quarterly with a GRC platform or policy management software. Look for age, repeats that signal vulnerability management gaps, expired approvals, and patterns by team, vendor, or process; automated alerts can help track nearing expirations. If staff keep bypassing intake rules for urgent matters, which undermines the core security policy, the answer may be better intake design, not more forgiveness. A single front door intake guide can help you separate necessary human judgment from silent policy drift.
FAQs about policy exception management
What’s the difference between an exception and a policy update?
A security exception is temporary and narrow. A change to internal standards updates the standing rule for everyone.
Who should approve policy exceptions?
It depends on the risk. Authorizing officials or the CISO should handle risk acceptance based on a formal risk assessment. Approvals should sit with a named owner, not whoever gets asked first.
How often should you review exception logs?
Quarterly is a solid minimum in risk exception management. Higher-risk areas may need monthly review to support information security maturity and effective risk exception management.
Can a small organization do this without special software?
Yes. Start with one formal request form, one owner, and one shared log backed by risk analysis. These steps matter more than tools for regulatory compliance. Discipline matters more than tools.
A policy exception is a useful tool. It becomes a problem when it replaces ownership.
Proper policy exception management starts with a clear exception request process, thoughtful risk acceptance, adherence to security policy, and proactive risk mitigation. This approach strengthens information security and avoids non-compliance. Submit your next exception request with care.
Start small this week. Pick one policy, count the active exceptions, and ask a hard question: are you managing exceptions, or are exceptions managing you?