A cybersecurity purchase is never just a security purchase. It is a business decision about risk, visibility, and control.
If you approve the wrong thing, you can end up with more tools, more alerts, and the same blind spots. If you approve the right thing, you should get cleaner reporting, faster response, stronger board confidence, and less guesswork in the room.
That matters because many companies already have vendors, IT staff, and security tools. They still do not have clear ownership or reporting leaders can trust. If that sounds familiar, start with a sharper view of what is actually broken before you sign anything. Build a Board-Ready Technology Risk View
Key takeaways
- Start with the problem, not the product. Weak ownership, unclear reporting, and vendor drift can look like a cybersecurity gap when the real issue is leadership.
- Tie every dollar to a business outcome. Security spending should reduce disruption, speed recovery, and make decisions easier to defend.
- Check the leadership structure first. If no one can own the risk, report on it, and follow through, the investment will struggle.
Start by naming the real problem, not just the tool you were sold
Before you approve anything, slow the conversation down. Ask what is actually driving the concern.
Sometimes the issue is a real cyber risk. Sometimes it is a process failure. Sometimes it is a governance problem wearing a security label. Those are not the same thing, and they do not call for the same fix.
A dashboard can make the situation look more serious than it is. A quiet team can make it look safer than it is. Neither one tells you much unless you know what is missing. Is it visibility? Response speed? Accountability? Control over vendors? Clear decision rights? That is the real question.
Separate true security gaps from reporting gaps
A bad report does not always mean a bad security posture. It may mean your team cannot explain risk in a useful way. That is a different problem.
You need to know whether the business lacks detection, response, ownership, or decision clarity. If no one can answer those questions in plain English, the investment review is too early.
A good test is simple. Ask what a leader would do differently after this purchase. If the answer is fuzzy, the proposal is probably fuzzy too.
Ask who will own the risk after the purchase
Every cybersecurity investment needs a named owner. Not a department. Not a vendor. A person who is accountable for the outcome.
That owner should know what they are responsible for, how progress will be measured, and when risk gets escalated. If that structure is weak before the purchase, the new tool will not fix it.
This is where executive technology leadership matters. Executive technology leadership is not about more activity. It is about clearer ownership, better decisions, and calmer follow-through when things get messy.
Watch for vendor-led decisions that solve the vendor’s problem
Vendors are useful. They are also paid to sell their version of the answer.
That means you need to test whether the proposal fits your actual risk, your actual priorities, and your actual operating capacity. If the pitch starts with features and ends with business impact, you are probably looking at the right thing in the wrong order.
Be careful when the roadmap follows the product catalog. Your company’s needs should drive the plan, not the other way around.
Measure the investment against the business outcomes you actually need
Cybersecurity spending should be judged the same way you judge any serious investment. Does it protect revenue? Does it reduce disruption? Does it help you move faster without taking dumb risks?
If the answer is no, you need to keep asking questions.
Good security reduces downtime, shortens recovery time, improves customer trust, and gives your board something they can understand. It also cuts the time your team spends chasing issues by hand. That is real value. So is fewer surprises.
Tie each security dollar to a risk you can explain in plain English
If you cannot explain the risk without jargon, you do not understand it well enough yet.
Try this instead. What happens if you do nothing? What is the likely business impact? What changes if you approve the investment? The answers should be concrete. Loss of customer trust. Longer outage recovery. More manual work. More exposure in a diligence review. Those are business terms leaders can act on.
The point is not to make cybersecurity simple. The point is to make it legible.
Look for proof that the investment will reduce drag, not add complexity
The best security work makes the business easier to run.
If the proposal adds duplicate tools, more handoffs, or extra approval steps without removing something else, be careful. More motion is not the same as more control. In some companies, security stacks become another layer of clutter.
A smart investment should simplify reporting, sharpen escalation, and reduce tribal knowledge. If it just creates more noise for your team, it is not ready.
Define what success will look like in 90 days and 12 months
You need two horizons.
In 90 days, what should be different? Maybe reporting is cleaner. Maybe unresolved alerts are down. Maybe ownership is no longer fuzzy. Maybe incident response is faster and less chaotic.
In 12 months, what should be different? You should be able to say whether board visibility improved, whether the team depends less on heroics, and whether the business is more prepared for pressure.
If nobody can define those outcomes, the purchase is not ready for approval. It is still a theory.
Check whether the company has the leadership structure to make the investment work
Even good cybersecurity tools fail when leadership is weak.
This is where many executives miss the real issue. The problem is not just the control. It is whether the company has enough executive oversight, enough decision clarity, and enough follow-through to make the control matter. Cybersecurity often exposes a broader technology leadership gap.
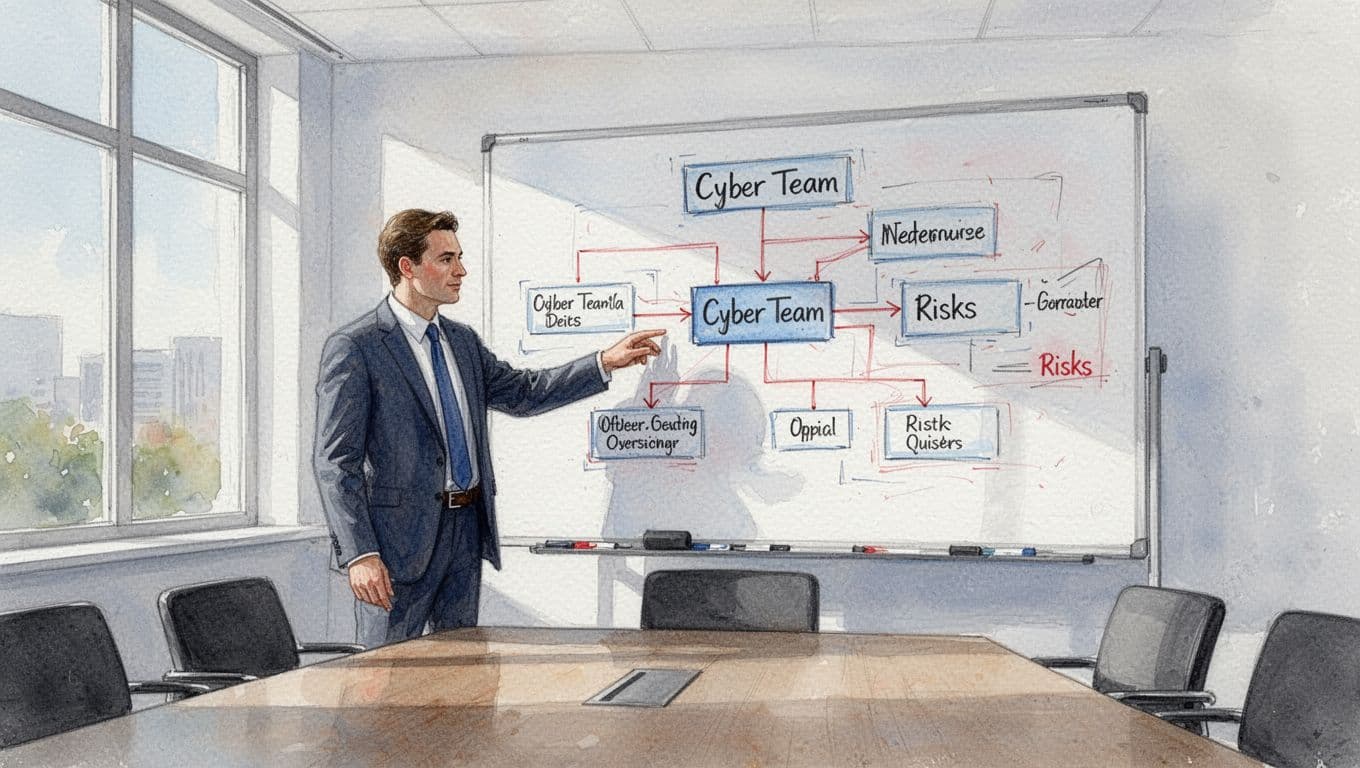
Decide whether you need fractional leadership, interim leadership, or better oversight
Not every situation needs a new leader in the seat. Some need a fractional CTO. Some need interim leadership. Some need stronger executive oversight over vendors, systems, and priorities.
The right support depends on the problem. If you need steady direction, a fractional model may fit. If the company is in a hard moment, interim leadership may be the better move. If the issue is mostly visibility and decision structure, oversight may be enough.
That is why a firm like CTO Input’s fractional CTO and interim services can be relevant when the question is bigger than one tool purchase.
Make sure your board reporting can show risk, progress, and tradeoffs
Boards do not need a flood of technical detail. They need clear signals.
Good reporting should show current risk, who owns each issue, what is improving, what is stalled, and what needs a decision. It should also make tradeoffs visible. If you fund one area, what slips? If you delay, what grows worse?
That is the kind of reporting that helps a board govern instead of react. If your current reports cannot do that, adding a security tool will not solve the problem.
Use a clarity call when the real issue is still fuzzy
If you are not sure whether you have a leadership problem, a reporting problem, an ownership problem, or a cyber risk problem, pause before approving the spend.
A simple diagnostic conversation can save you from buying the wrong thing for the wrong reason. It can also show you whether the next step is leadership, reporting, process, or the investment itself. Talk Through Your Technology Leadership Gap
Ask the questions that separate a smart investment from an expensive mistake
You do not need a longer checklist. You need better questions.
Start with these.
- What risk are we reducing, and how will we know it changed?
- What will this replace, simplify, or retire?
- What will we need to change internally to make it work?
- Who owns it if the outcome is not improving?
Those questions force the conversation out of sales mode and into operating reality. If the answers are vague, the investment is not ready. If the answers are clear, you can approve, reject, or reshape the proposal with more confidence.
One more question matters. If this fails, what breaks first? That tells you whether the business is ready for the change or just hoping the tool will carry the load.
FAQ
Is every cybersecurity investment worth approving?
No. Some are necessary, some are premature, and some are just expensive ways to avoid a harder leadership problem. Judge the investment by the business risk it reduces, not by how urgent the pitch sounds.
What if the board wants more security spending right away?
Then you need to show the board what problem the spend solves, who owns it, and how progress will be reported. Boards usually want stronger control, not more noise. Give them that.
What if we already have IT or a security vendor?
That still does not mean you have executive ownership. Vendors and internal teams can do a lot. They cannot replace leadership judgment, clear reporting, or decision rights.
Conclusion
The best cybersecurity investment is not the one with the longest feature list. It is the one that reduces real risk, fits your operating capacity, and gives leadership better visibility.
If the problem is still fuzzy, do not hide it behind a purchase. Get clear on ownership, reporting, and the actual business risk first. That is how you avoid buying more tools and calling it progress.
If you want a sharper view before you approve the spend, Get an Executive Technology Clarity Check.

