Practical resources
for justice operations,
data, and digital trust
Practical guidance for mission-driven executives who need clearer systems, cleaner data, and lower privacy risk so they can move faster with confidence.
Nothing exposes weak reporting faster than a new funder scorecard. When a funder changes what it wants, your old board pack can fail in one cycle. Definitions drift, staff rebuild numbers by hand, and your board gets a packet full of motion but not much
- CTO Input
A grant pays for a pilot, the team likes it, and the renewal slips into next year’s budget. That sounds harmless, until tool sprawl starts running your operations. You end up with extra logins, duplicate data, side workflows, and reports nobody fully trusts. Managing multiple
- CTO Input
SEO title: A Technology Roadmap That WorksMeta description: A practical guide to building a technology roadmap that works by clarifying ownership, decision rights, and review cadence so execution becomes predictable.Slug: technology-roadmap-that-works Growth makes technology problems harder to hide. You see it when every leadership meeting
- CTO Input
One side-door request rarely feels like a problem in a group home. Then the requests start arriving by text, email, Slack, hallway conversation, and board introduction, and your intake process stops being a process. When work enters through private channels, triage gets weaker, fairness drifts,
- CTO Input
Growth is supposed to feel like progress. Yet for many founders and CEOs, it just exposes technology problems that were easy to ignore at a smaller stage. The result is a slow, grinding frustration. Key projects stall, your team seems to be in a constant
- CTO Input
Referral partnerships depend on social connections built through clear digital communication. A referral that disappears is worse than a slow one. When a partner stays silent, your team starts guessing, clients wait longer, and staff reopen work they thought was done. Different professional attachment styles
- CTO Input
If you have ever felt the air go still in the boardroom after a simple question like, "How secure are our most critical vendors?" you know the feeling. That moment of hesitation is more than just an awkward silence. It’s a signal that your approach
- CTO Input
Buying a new matter management software feels like action. It gives you a budget line, a vendor demo, and the hope that intake will finally calm down. But legal intake chaos rarely starts with software. It starts with legal operations handling too many entry points,
- CTO Input
Growth often exposes technology problems that were easy to ignore at a smaller stage. The systems that felt efficient a year ago now seem to create friction, slow down projects, and drain resources. If you have a nagging feeling that you are pouring money into
- CTO Input
You lead a legal aid or justice organization. Intake forms pile up with details you rarely use. Staff ask the same questions twice. Client data spreads across tools. Privacy risks grow quietly. Boards and funders notice the scramble in reports. You lose time, trust, and
- CTO Input
If your team is busy but key initiatives keep stalling, the problem may not be your people. It might be a fundamental confusion between policies and procedures. When leaders can't distinguish between the two, they create operational drag that burns out teams, slows growth, and
- CTO Input
You send out referrals every day. Clients need help from partners. You log them as successes under open-loop attribution. But weeks later, you hear nothing back. Those vanity metrics look good in reports. They do not show the truth. People still fall through cracks. Funders
- CTO Input
Growth often exposes technology problems that were easy to ignore at a smaller stage. If technology has become expensive but leadership cannot explain what it is doing for the business, you have a leadership problem, not a technology problem. Without clear technology leadership, it is
- CTO Input
You run a legal nonprofit where cases stack up fast. Staff track intake, handoffs, and mission-critical client outcomes in scattered Excel files. These shadow spreadsheets feel like a quick fix. They hide in emails and shared drives. Yet they slow your team, weaken reports, and
- CTO Input
A technology strategy is not just another document to file away. It is an execution system designed to connect what you spend on tools and people to actual business results. Think of it as the framework for making decisions that ensures your technology builds momentum
- CTO Input
A suspected third-party vendor breach can turn a normal morning into a leadership test in minutes. The hard part is that you won’t have clean facts yet, but people will still want answers right away. Your goal in the first 30 minutes isn’t to explain
- CTO Input
Growth has a way of exposing every hidden crack in your technology foundation. As a CEO, founder, or board member, you might be feeling the tension. Projects are delayed, your team is burned out from constant firefighting, and the technology that was once an asset
- CTO Input
A policy exception should be rare. When it shows up every week, it stops being an exception and starts becoming your real operating model. That shift is easy to miss because each exception feels reasonable on its own. Yet over time, side deals, one-off approvals,
- CTO Input
Rapid growth has a funny way of exposing every crack in your technology foundation. Problems you could once ignore suddenly become business-critical emergencies. This is where an interim CTO comes in—not as a temp hire, but as an experienced executive brought in to fix urgent
- CTO Input
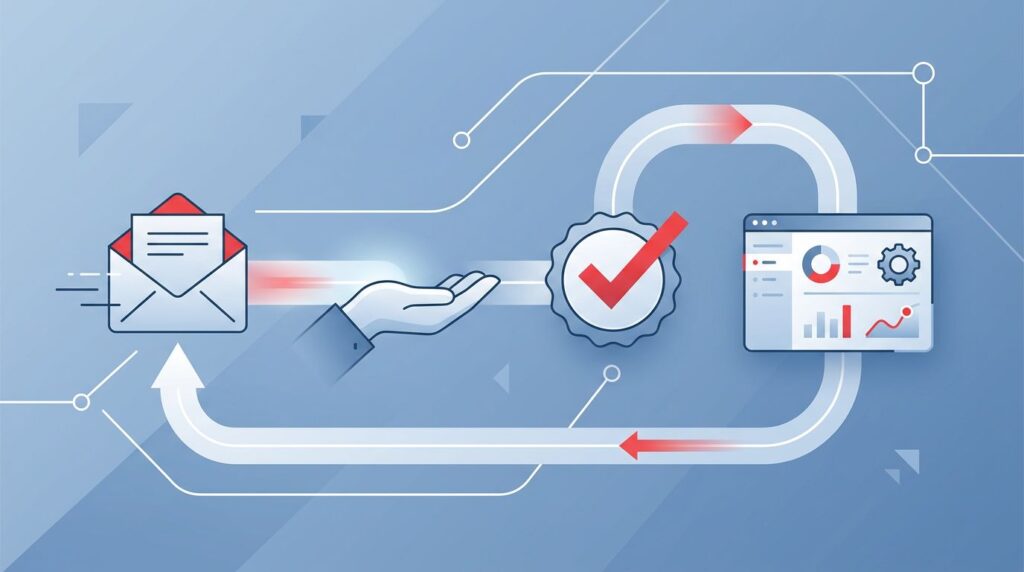
Every team inbox, often set up as a shared intake group email address, starts with good intentions. Then volume rises, side replies multiply, and nobody can say who owns the next move. That is why shared inbox management often breaks down in plain sight. The
- CTO Input
Growth often exposes technology problems that were easy to ignore at a smaller stage. If your business feels like it is running on adrenaline but not moving forward, the problem might not be your team. It is often a sign of a missing link: strategic
- CTO Input
Audits rarely go sideways because of one missing file. They go sideways because work that should have happened in March gets noticed in September. That’s why a control owner calendar matters. It provides the calendar management needed to turn scattered reminders, half-owned tasks, and stale
- CTO Input
Growth often exposes technology problems that were easy to ignore at a smaller stage. If projects are stalling, budgets feel like a black hole, and the board is asking harder questions about risk, the problem is not just technology. It is a leadership gap. A
- CTO Input
In animal shelters, broken handoffs rarely look dramatic at first. A case waits in the wrong queue. A referral gets sent but never confirmed. Someone assumes the next step belongs to someone else. Then the cost shows up, impacting animal welfare. Clients repeat their story.
- CTO Input
If you find your teams constantly putting out fires, watching projects drag on, and blowing past budgets, the problem might not be your people. The chaos is likely coming from outside—from a sprawling, unmanaged web of vendors that now sets the pace for your entire
- CTO Input
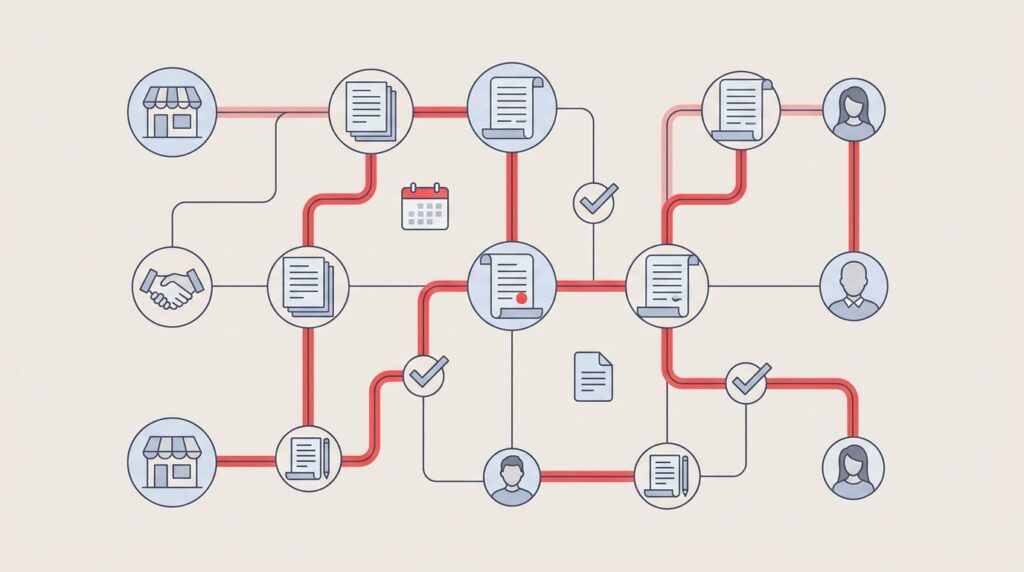
A contract doesn’t have to be bad to hurt you. It just has to renew quietly while nobody notices the notice window closed. That is why a contract owner map matters. It gives you one clear view of the source contract owner for each vendor
- CTO Input
You know the feeling. That critical project—the new system migration, the security overhaul—is stuck. Your team is burning out in endless meetings. Leadership is getting frustrated with vague updates. And the game-changing results you were promised feel further away than ever. The problem is not
- CTO Input
Every leadership team knows the pattern despite internal controls meant to manage routine purchases. A routine purchase starts small, then bounces between program, finance, operations, and the executive team. Days pass. Nobody feels clearer. Meanwhile, the real work slows down. A spending threshold matrix, or
- CTO Input
Why does the same case get three different answers on three different days? In legal aid, that usually means your rules live in people’s heads instead of in one shared system. A legal aid rules matrix gives you one place to define what you accept,
- CTO Input
When the same system outage grinds business to a halt for the third time this quarter, the frustration in the leadership team is palpable. The immediate reaction is often to ask who dropped the ball, but the real failure is almost never a person. It
- CTO Input
The chaos in your tech and security teams is not because you have the wrong people or haven't bought the latest tools. The problem is simpler and more costly: your decisions are made without clear owners, forcing your best people to operate in a system
- CTO Input
You’re running on assumptions about your donor and client data. That nagging sense of dread is real. It’s the cost of invisible risk and fuzzy ownership. A single mistake with a spreadsheet or a vendor problem can erode decades of trust you’ve worked to build.
- CTO Input
You have a business continuity plan. It was probably created for an auditor or an insurer. It sits on a shelf, a digital artifact of compliance, costing you silent risk every day it goes untested. When a real crisis hits—a key vendor goes down, ransomware
- CTO Input
The ransomware bill always comes due. You just get to choose when, and how, you pay. You can pay in advance through calm, deliberate preparation, or you can pay a much higher price later, in the chaos of a live attack, with your reputation, customer
- CTO Input
Your technology roadmap isn't yours anymore. It's a patchwork of vendor release cycles, aggressive sales promises, and "urgent" upgrades you're paying to maintain. The cost is more than money. It's the constant chaos, the project delays, and the sense that you are reacting, not leading.
- CTO Input
The contract is over. The final invoice is paid. But months later, you discover the vendor is still in your systems. Not with a password, but through a forgotten API key or an orphaned service account. This isn't a rare oversight; it's a systemic failure.
- CTO Input
Your last board meeting felt off. You presented a deck full of cybersecurity metrics, but the room went quiet. Then came the question that hangs in the air after every one of these updates: “Are we actually secure?” The honest answer is you don’t really
- CTO Input
Your audit committee meetings feel like a recurring nightmare. Smart people present complicated slides, but the core questions remain unanswered: Are we secure? How do we know? This isn't a failure of your team. It’s an operating system problem. When technology and security are misaligned,
- CTO Input
You closed the deal. The financial models looked solid. But three months post-acquisition, the portfolio company’s tech team admits they cannot patch a critical vulnerability without risking a core system outage. The real cost of inadequate cyber diligence is not just a potential breach. It
- CTO Input
Another quarter, another fire drill. An auditor, a new cyber insurance renewal, or a potential investor is asking questions you can't answer cleanly. "Can we prove who has access to customer data?" "What's our plan if a key vendor has a breach?" "How fast can
- CTO Input
Your board is tired. They are tired of slogging through dense, technical reports that leave them with more questions than answers. They see alarming headlines about cyber threats, turn to you for assurance, and ask a simple question: "Are we safe?" The cost of getting
- CTO Input
Your nonprofit holds sensitive information. From donor financials to confidential client records, this data is the lifeblood of your mission. But who, specifically, is accountable for protecting it? If you can’t name one person, you’ve just found a critical risk. It's a vulnerability that has
- CTO Input
If your team keeps adopting new tools while projects remain stuck, you’re not alone. You see the pattern: everything is urgent and nothing finishes. Smart people are working hard, but chaos, fuzzy deadlines, and dropped handoffs are the norm. You assume the problem is the
- CTO Input
Your team is smart. You have invested in security tools. Yet projects stall, vendor risk climbs, and the board is asking questions you cannot answer cleanly. The chaos feels like a constant state of fire drills. Everything is urgent and nothing ever truly finishes. You
- CTO Input
You keep buying security tools, but the mess stays. Access permissions multiply with every new hire, contractor, and software tool, creating a web of invisible risk that quietly taxes your business. When an employee leaves, you hope their access is fully revoked, but you lack
- CTO Input
Your best people are exhausted, critical projects are stalling, and "everything is urgent" has become the daily mantra. You’ve tried wellness programs, but the burnout persists. This isn't a personnel problem. It's an operating system failure. The chaos, delays, and friction are symptoms of a
- CTO Input
You have smart people. You have expensive tools. You even have policies. So why are you still stuck in a cycle of constant fire drills, audit panics, and the nagging feeling that you are one click away from public embarrassment? The cost is real. You
- CTO Input
The uncomfortable truth is you are paying for enterprise architecture tools, yet chaos persists. You face ballooning tech costs, surprise risks, and delayed projects. Your teams are busy creating diagrams, but the boardroom remains blind to the real state of technology. The cost is immense:
- CTO Input
You keep paying for IT infrastructure management tools, yet the chaos continues. Alerts are noisy, ownership is fuzzy, and when something breaks, 'everyone' is responsible, which means no one is. Your team is smart and works hard, but they are drowning in a system where
- CTO Input
Your teams look busy, but critical projects are delayed. You have a gut feeling you're paying for dozens of software tools no one uses, but getting a straight answer on what can be shut down is impossible. Every vendor contract renewal feels like a gamble.
- CTO Input
You keep paying for smart people and good tools, but the mess stays. Your teams are busy, but nothing important ships. Deadlines slip, budgets bloat, and every new project feels like a fire drill. This isn't a sign of a bad team. It's the cost
- CTO Input
You see projects dragging. You watch handoffs get fumbled. Every problem escalates into an all-hands fire drill. You hired smart, capable people and bought good tools, so why does it feel like your organization is running in mud? This is not a people problem. It’s
- CTO Input
The annual audit is done, but the auditors won't issue their opinion. Everything grinds to a halt. Your board starts asking pointed questions. What's the holdup? A single, missing document: the management representation letter. This isn't a friendly suggestion; it's a hard stop. This letter
- CTO Input
You're tired of the chaos. Project delays, constant rework, and a creeping sense of risk have become the norm. Your teams are working hard, but it feels like they’re running in place. When everything is urgent and nothing ever seems to get finished, you’re not
- CTO Input
It's a familiar pattern: another urgent project stalls, another security audit reveals gaps, and another key deadline is missed because of a self-inflicted outage. You have invested in smart people and powerful platforms, yet the day-to-day reality is a series of fire drills. You keep
- CTO Input
A formal change management process is, at its core, a structured way to get your teams, projects, or even your entire organization from where you are now to where you need to be. It is not about managing feelings. It is an operating system for
- CTO Input
A grant report is due, the coalition call is in two hours, and someone asks the question you dread: “Why don’t these totals match?” In justice networks, that moment is common. Legal aid, courts, navigators, and community partners each track the work in good faith,
- CTO Input
Let’s be direct. Your organization is swimming in data, but you can’t trust it, find it, or prove it’s secure. Your teams are arguing over whose report is right, and major projects stall. The cost of this chaos is real, measured in wasted hours, delayed
- CTO Input
An operational resilience assessment for legal aid organizations, centered on legal aid operational resilience, is a plain-language review of what keeps services running when something goes wrong. It focuses on the real chain of work, from first contact to case outcomes, and conducts a business
- CTO Input
You keep hiring smart people and investing in the latest tools, but the chaos doesn't stop. Projects are behind, every task feels urgent, and the near-miss incident last week was a stark reminder of how fragile your operations are. This isn't a people problem. It's
- CTO Input
Monday morning, the self-help queue is already full. A kiosk is down, the forms site is slow, and staff are doing the same intake twice because two systems don’t match. By lunch, someone’s built another spreadsheet “just for this week,” and the reporting deadline is
- CTO Input
The annual scramble to prepare for an audit is a symptom of a deeper problem. It’s a recurring fire drill where teams hunt for evidence, rewrite policies, and hope auditors don’t ask the one question nobody can answer. This last-minute chaos isn't just stressful, it's
- CTO Input
The intake queue is exploding. A partner needs records today. A funder report is due, and your team is already stretched thin. In the middle of that, digital security can feel like an extra project. For civil justice system organizations and civil society organizations (legal
- CTO Input
Your disaster recovery plan is likely a document, not a system. You have smart people and expensive backup tools, but when a real disruption hits, your team is left guessing. Without a clear, pre-agreed deadline for restoring services, every action is a scramble. This chaos
- CTO Input
In December 2025, court services organizations are carrying heavy demand with public consequences. People expect e-filing to work, remote hearings to connect, and self-help services to be available when they need them. There’s almost no tolerance for downtime, and no slack in the staffing model
- CTO Input
Another quarter, another near-miss. A key system flickers, a critical vendor has an outage, or a senior engineer quits with two weeks’ notice. Your team scrambles. They pull all-nighters, burn favors, and through sheer heroics, they keep the lights on. This feels like a win,
- CTO Input
A survivor reaches out from a borrowed phone. Your intake team moves fast, because timing matters. Then a simple mistake lands hard: an advocate auto-forwards an email thread, it goes to the wrong address, and suddenly a client’s location and case details are exposed. In
- CTO Input
Your disaster recovery plan is likely a document, not a capability. It sits in a shared drive, untouched since the last audit, creating a dangerous illusion of safety. When a real crisis hits, this document will fail. Your team will scramble, customers will suffer, and
- CTO Input
Your intake queue is exploding, a training partner needs an export by Friday, and a funder report is due with numbers that don’t reconcile. Then a vendor emails, “We updated our platform with new AI features.” Your team didn’t ask for that. Now it’s your
- CTO Input
You have binders, spreadsheets, and Word documents labeled 'Business Continuity Plan.' Smart people wrote them. Yet, when a vendor goes down or a key system fails, the response is a frantic scramble. The plans are static, disconnected from daily operations, and useless for proving readiness
- CTO Input
Your intake queue is climbing. A partner wants an answer today. A funder report is due, and the numbers don’t tie out. Then the executive director change happens, and every open thread suddenly feels urgent. In an executive director transition, the hidden risk isn’t only
- CTO Input
Your intake queue is overflowing. A partner needs access to a shared platform today. A funder due diligence form lands in your inbox, asking about encryption, vendor risk, and incident response, with a deadline you can’t move. In capacity building organizations, you’re not only protecting
- CTO Input
That thick binder labeled "Business Continuity Plan" on your shelf? It’s a liability. You paid a consultant or tasked a team to create it. You pull it out for audits. But when a critical system actually goes down at 2 a.m., no one reaches for
- CTO Input
You know the moment in non-profit organizations dedicated to capacity building. A report is due, a funder wants clean numbers, and three program leads send three different versions of “served” and “completed.” Staff scramble. Someone rebuilds a spreadsheet late at night. The numbers still don’t
- CTO Input
You have a thick binder on the shelf labeled "Crisis Plan." It feels like you're prepared, but when a real crisis hits—a system-wide outage, a major vendor breach, or a supply chain collapse—that static document is the first casualty. The frantic, late-night calls begin, and
- CTO Input
Your navigator team didn’t get hacked, but a vendor did. Now your intake tool is down, texting is unreliable, or a cloud folder with client documents might be exposed. This sparks an incident response scramble. Staff are asking what to say. Courts and partners want
- CTO Input
The grant report is due, and the numbers don’t reconcile. Program data is split across tools, and security updates live in a separate world. Someone asks, “Are we safe?” and the only honest answer feels like, “I think so.” This is where an executive-level cyber
- CTO Input
Your team is smart. You’ve invested in tools. Yet, every technical issue seems to escalate into an all-hands fire drill, derailing projects and eroding the trust of customers and your board. The alerts never stop, ownership is fuzzy, and decisions made under pressure don’t stick.
- CTO Input
Investors are tired of hearing the same pitch: “We’re moving to the cloud, using AI, and modernizing systems.” Most of those pitches blur together or collapse into jargon. What stands out is not the stack, it is the story behind it. For a non-technical CEO
- Tyson Martin for CTO Input
That late-night alert isn't just a technical problem. It’s the start of a frantic, middle-of-the-night scramble that pulls executives into chaotic calls and ends with fumbled answers to your board and insurers. You keep paying for new security tools, but the mess stays the same.
- CTO Input
If your legal aid intake queue is exploding and a funder report is due, nonprofit cybersecurity can feel like a “later” problem. Until an account takeover locks you out of email, a ransomware note freezes a shared drive, or a data leak puts a client
- CTO Input
An incident response readiness assessment is not another report to file. It is a live-fire exercise that reveals the dangerous gap between the plan in your binder and what your team can actually do when a crisis hits. It is the only way to shift
- CTO Input
Legal aid organizations face a constantly growing legal aid intake queue, which undermines access to justice for those who need it most. Requests arrive by phone, web, email, walk-ins, partner referrals, even social media. Staff do their best, but urgency gets missed, notes end up
- CTO Input
You’ve invested in smart people and expensive security tools, yet the organization’s biggest vulnerability is still a single, unintentional click. A clever phishing email is all it takes to derail strategic projects, consume leadership's time with fire drills, and shatter the trust you've worked hard
- CTO Input
You already know AI is in your company. Sales is pasting customer data into chatbots. Finance is testing spreadsheet add-ins. Your vendors keep pitching “AI-powered” features. Without guardrails, every one of those experiments can turn into a data breach, a compliance headache, or a disappointed
- Tyson Martin for CTO Input
The intake queue is exploding. A court partner sends walk-ins, like those seeking housing legal help, you didn’t expect. Your hotline script is different from your online form. Staff spend half the day re-asking the same questions, then trying to “place” cases through a chain
- CTO Input
On Monday, intake is exploding. On Tuesday, a partner says they never got the referral packet. On Wednesday, a funder report is due and the numbers don’t reconcile. By Friday, someone says, “We should fix the system,” and everyone nods, because it’s true. Then nothing
- CTO Input
The renewal email lands in your inbox when intake is already backed up, a report is due, and a vendor just changed their portal again. Now your broker wants answers fast. Multifactor authentication? Backups? Incident response plan? Vendor controls? You know the work is happening,
- CTO Input
You've invested in firewalls, endpoint protection, and maybe even a powerful SIEM system. Yet, the nagging feeling of exposure won't go away. Your board is asking tougher questions, your cyber insurer wants proof of control, and every near-miss feels less like a win and more
- CTO Input
The moment you suspect a security breach, the room changes. Phones ring. Someone’s email “did something weird.” A partner asks if they should stop sending referrals. Staff are scared, because clients could be at risk. In justice work, a breach isn’t just an IT problem.
- CTO Input
Switching the team that runs your company’s IT is a little like changing the tires on a moving car. It’s possible. It’s common. It can also go sideways fast when nobody owns the plan. If you’re switching MSPs, your real goal isn’t “a better provider.”
- Tyson Martin for CTO Input
Hook: Chaos Costs Millions and Erodes Trust Last quarter a finance leader learned that a third-party marketing plugin exposed customer data. The unexpected breach froze projects, drained budget, and shook the board’s confidence. The true cost wasn’t the plugin fee or the legal bill. It
- CTO Input
The intake queue is already too long. A court deadline is already too close. Then someone says the words that make your stomach drop: files are locked, systems are down, a ransom note appeared. For legal aid, court self-help, navigator programs, and justice-support nonprofits, Ransomware
- CTO Input
The SaaS tool renewal you just auto-approved is more than a line item. It’s an open door into your network, your data, and your customers' trust. Third-party vendor risk management is the discipline of ensuring those doors are managed with intention, not left open by
- CTO Input
On paper, the deal looks perfect. The financials are solid, the market opportunity is clear, and the legal review is clean. But a multi-million dollar surprise is often buried in the target's technology, a quiet liability waiting to detonate right after you close. Suddenly, a
- CTO Input
Most companies don’t get breached because they “forgot security.” They get breached because passwords spread like loose change, pockets, couches, backpacks, old laptops, and the one shared spreadsheet everyone swears is temporary. A strong enterprise password manager is one of the fastest ways to reduce
- Tyson Martin for CTO Input
The intake queue is exploding. A key partner is asking for an update you don’t have yet. Your case management system is slow or down. A court deadline is coming fast. Everyone’s working hard, but work keeps bouncing between inboxes, spreadsheets, and hallway conversations That’s
- CTO Input
It’s 4:45 p.m. Intake is backed up. A partner asks for a file “right now.” Finance needs numbers for a funder update. Then someone forwards a strange email that looks like it came from a court address, underscoring the operational security challenges nonprofit organizations face
- CTO Input
The intake queue is exploding. A partner needs a same-day handoff. A funder report is due, and the numbers don’t reconcile. In that pressure, privacy turns into a cleanup job. A rushed form. A shared spreadsheet. A “temporary” folder that becomes permanent. For justice nonprofits
- CTO Input
It’s 4:30 pm. A funder metrics request lands with a deadline you can’t negotiate. Someone exports “the list” from the case system. Someone else exports a different list from a different screen. A third person has the “real” numbers in a spreadsheet tab named FINAL_v7.
- CTO Input
Search Leadership Insights
Type a keyword or question to scan our library of CEO-level articles and guides so you can move
faster on your next technology or security decision.
Request Personalized Insights
Share with us the decision, risk, or growth challenge you are facing, and we will use it to shape upcoming articles and, where possible, point you to existing resources that speak directly to your situation.